

Welcome to the Hardenize blog. This is where we will document our journey as we make the Internet a more secure place and have some fun and excitement along the way.
Hardenize began with hostname-based scanning, meaning we would build an inventory of domains and subdomains—mostly via our automated discovery—then continuously monitor the IP addresses behind the known names. That actually works very well, especially given the rise of virtual hosting, where many services can be hosted on the same port but with different configuration. This is critical, for example, for our ability to discover all deployed certificates. Although name-based scanning has served us well, in order to further improve the visibility of our customers' systems, we've now added support for traditional network scanning.
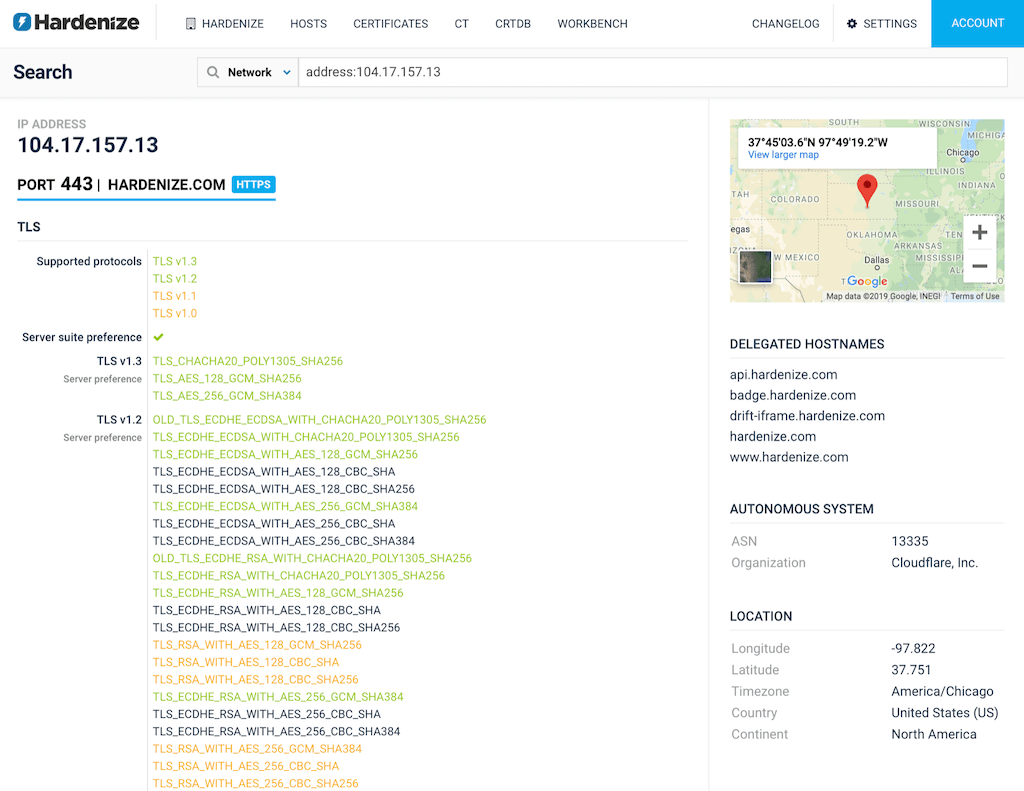
Starting with today, our customers can configure the network ranges that belong to them, and we will scan them on a daily basis. We use the 1,000 most popular TCP and UDP ports. The speed of scanning is adjusted so that our activity is not intrusive and that we're sending our traffic at the slowest possible rates. We support only IPv4 today, but IPv6 will be added in the near future.
In addition to discovering open ports, we perform protocol detection, fetch banners, as well as inspect TLS and PKI configuration. All the data is then imported into the same data model that we have for the rest of our monitoring activities.
As of today, we understand the following protocols:
We will continue to add support for new protocols as we see them in our customers' data.